Integrate.io for Data Security
No credit card • Full Trial for 14-Days
Prevent Data Breaches
-
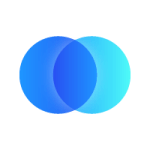
Secure TransformationsIBM estimates the average recovery cost of a data breach is $3.86 million. Integrate.io minimizes the risk to data in transit by hiding or removing sensitive information. Protect your PII data with Integrate.io.
-
Data EncryptionThe ultimate protected data is data that hackers can’t see. Integrate.io partners with Amazon's Key Management Service (KMS) to enable Field Level Encryption (FLE). With FLE, data is always encrypted when it leaves your network. Decryption is impossible without the key, which you hold on your side.

Because we integrate with so many different tools and technologies, our analytics data is stored in so many different places. Being able to pull that into a central location and summarize it in a way that is understandable by our customers is critical to us.
Improve Your Data Security
-
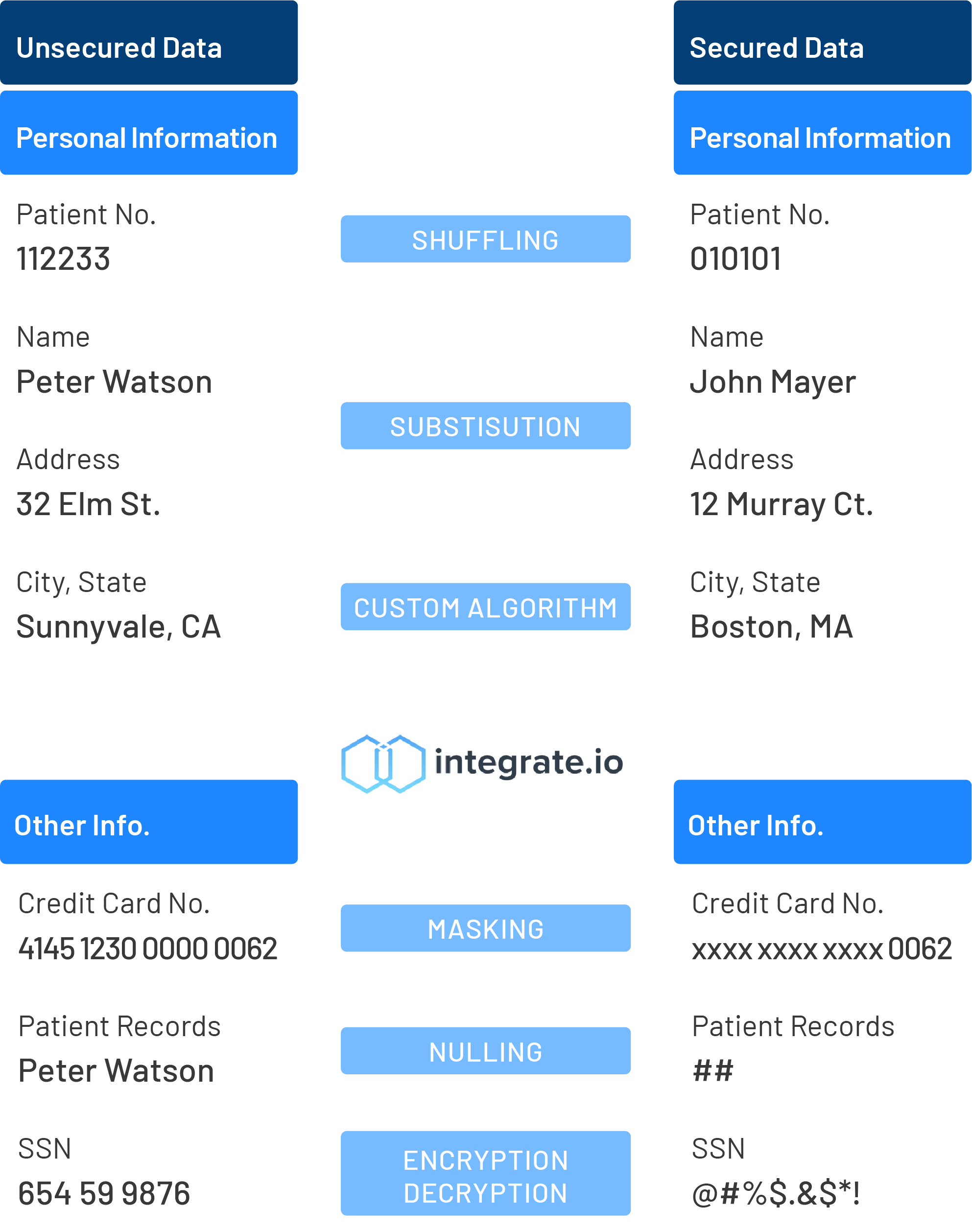
Ensure ComplianceThe E.U. has successfully fined a number of firms up to $11.03 million for breaking compliance laws, including Google. Integrate.io is GDPR, HIPAA, CCPA, and SOC 2 compliant. Stay in compliance with data privacy and protection laws with Integrate.io.
-
Enterprise Security Features85% of cyber attacks come through well-intentioned employees. Ensure you aren’t the cause of your company’s data breach with advanced Integrate.io security features like - data masking, hashing, SSH tunnels, two-factor authentication, and more.
Common Integrations
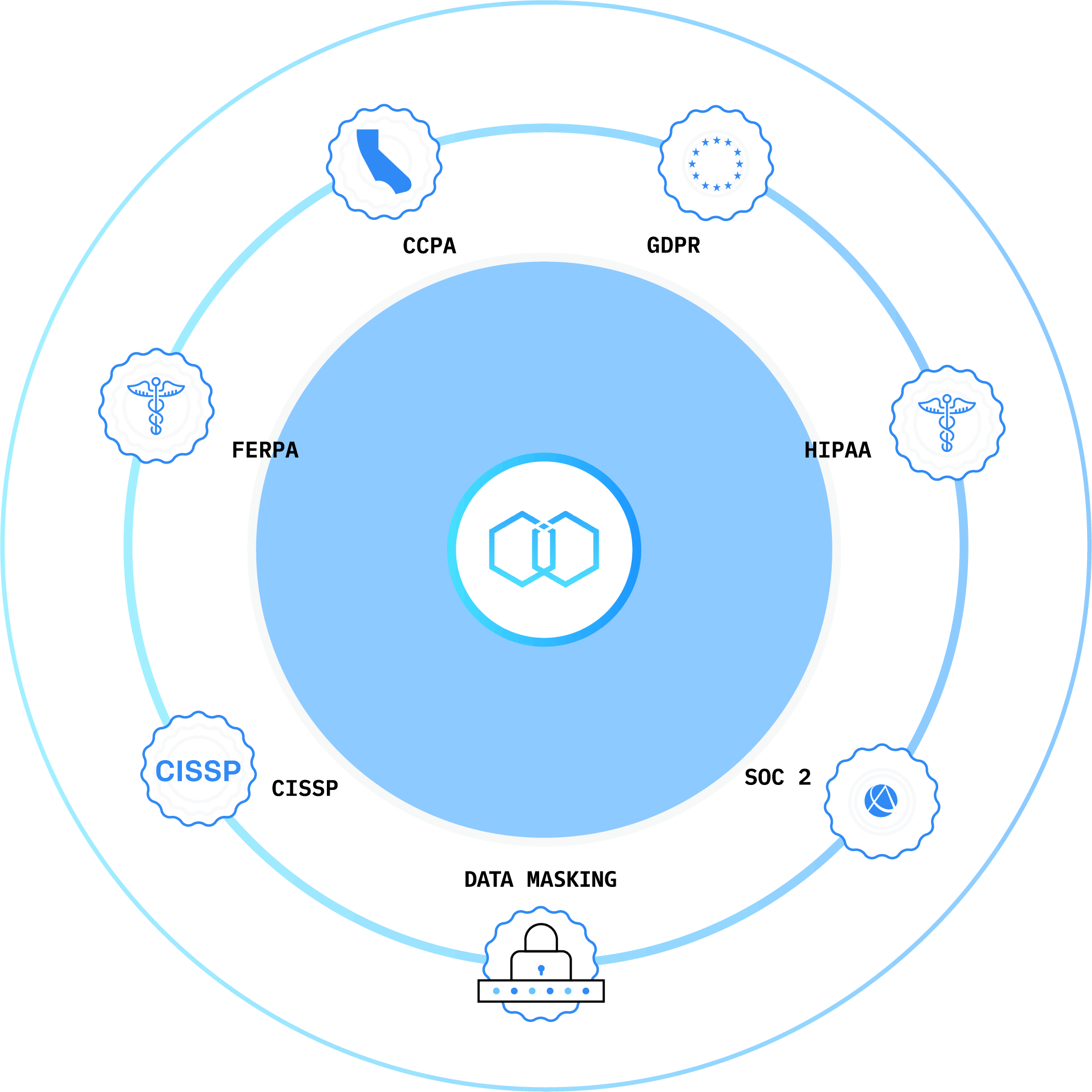
Painless and Secure Transformations
-
Focus on Your Core BusinessYou need to safely move large amounts of data between systems, but just one data point takes too long. Integrate.io's pre-built data sources and destinations make it fast and easy to deploy. Reduce the time it takes to load your datasets by up to 95% with Integrate.io.
-
Integrate.io Security TeamWe have CISSP and Cybersecurity-certified members on our Security team that will help you create and implement your data security strategy. We also use SSL/TLS encryption on all our websites and microservices in order to maintain the highest security and data protection standards.

Before Integrate.io... every Monday, our consultant was spending 3 ½ hours to manually do the reporting. It was insane. With Integrate.io, any analysis I want to do is just instant. It’s like a little miracle every day.
See how Integrate.io’s security compares to our competitors
Cloud ETL is a competitive market. You’ll find plenty of options out there, each with its own pros and cons. In this guide, get objective information from G2 about four of the best ETL providers in 2021: Integrate.io, Talend, Mulesoft, and Informatica.
Read the Report
The Unified Stack
for Modern Data Teams
Get started now to ensure your data is secure and compliant.