The steps below will guide you on how to set up Integrate.io ELT Secure VPN Tunnel for RDS and Redshift
On Integrate.io ELT & CDC, we currently offer two ways to set up a secure tunnel: through a template in CloudFormation or through a bash installation script.
The CloudFormation template is recommended because it requires minimal input from the user, and all the necessary services, configuration, and infrastructure will be created automatically. However, if you do not wish to use AWS or have a secure tunnel already set up, please use our Bash installation script.
1. On your dashboard, select Create a new tunnel. Choose a region where the secure tunnel instance will be launched and set a name for the secure tunnel. Click Download CloudFormation template
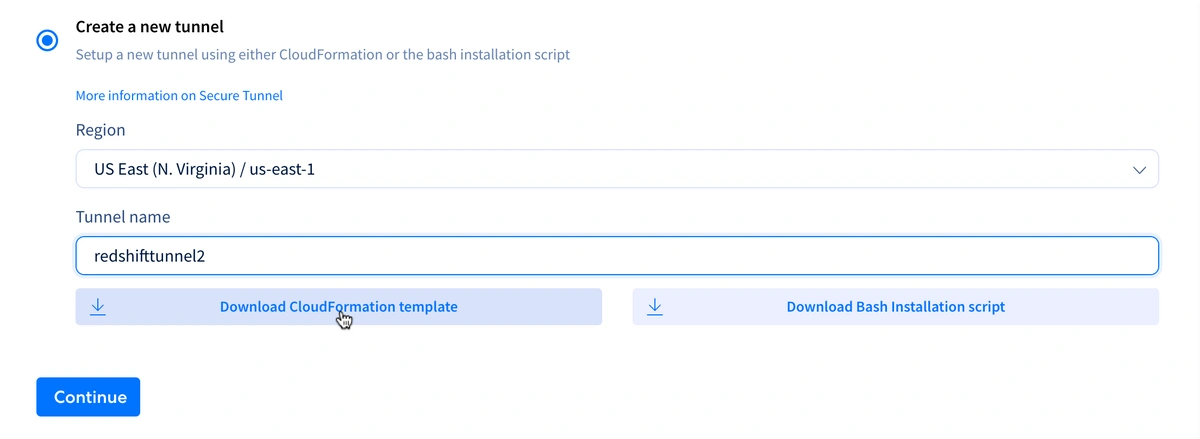
Note: You may use your existing tunnel if you already have an active one.
2. On your AWS page, go to CloudFormation > Stacks > Create stack > With new resources (standard)
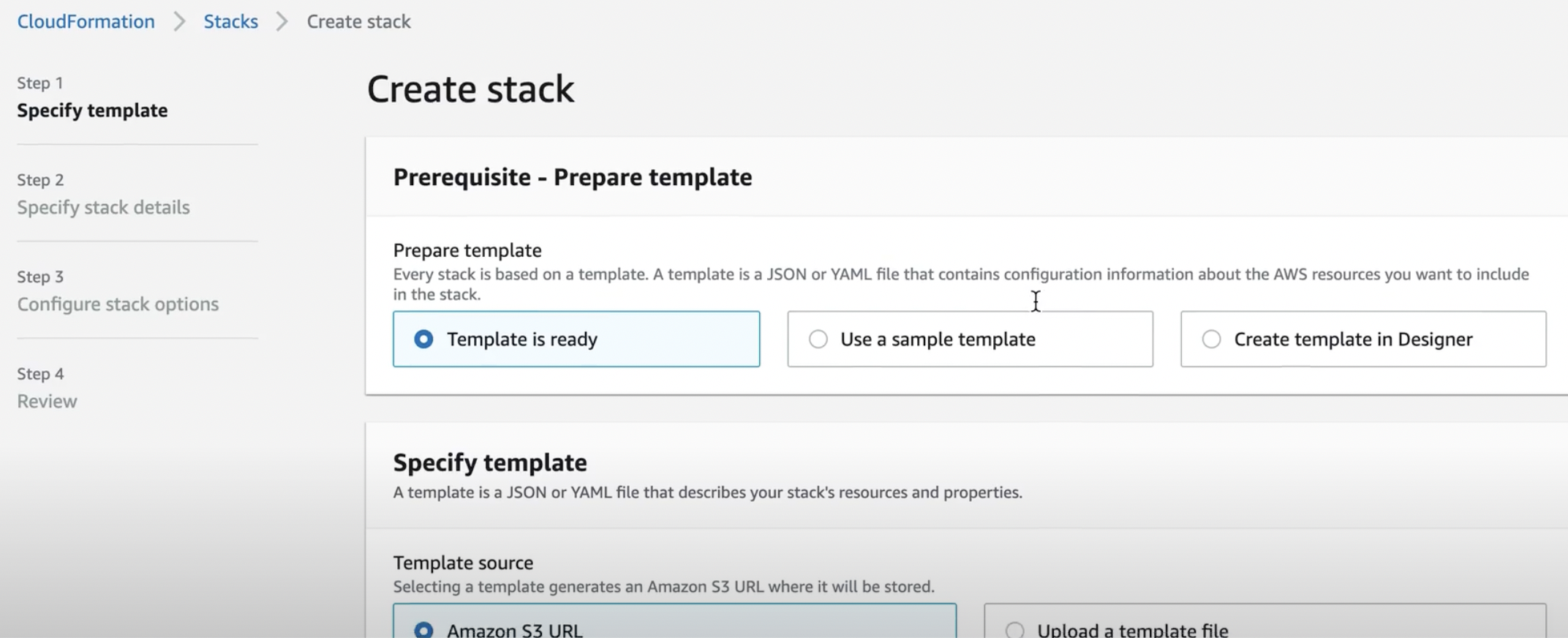
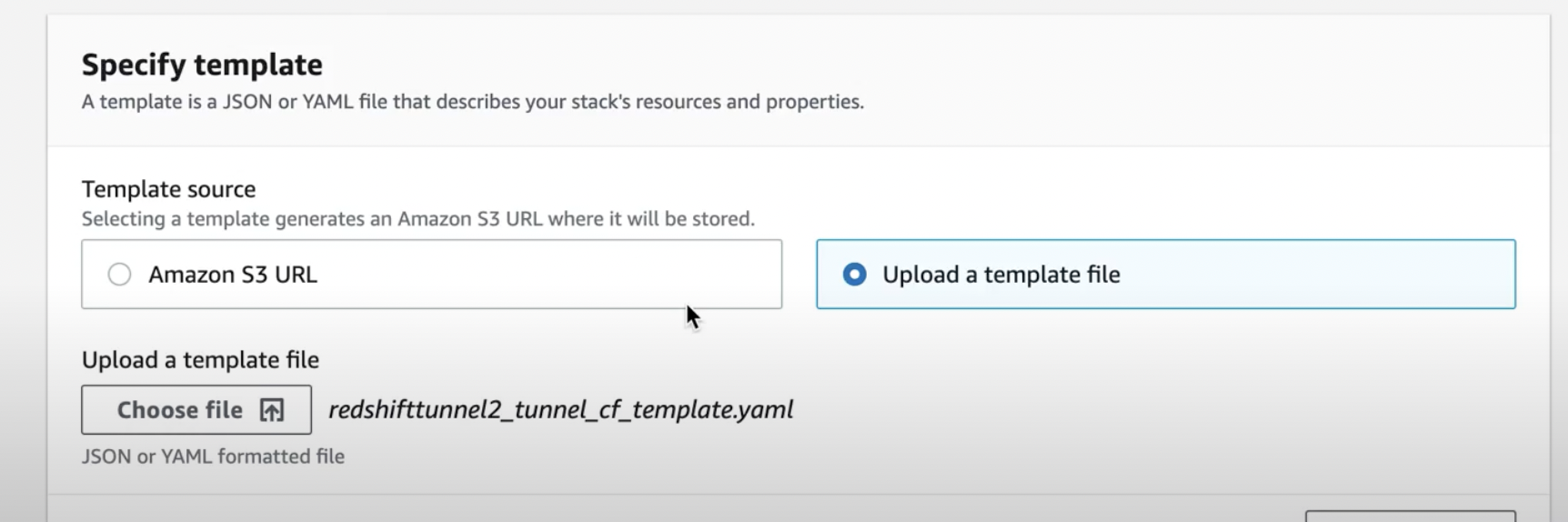
3. Upload the template generated by the Integrate.io ELT dashboard.
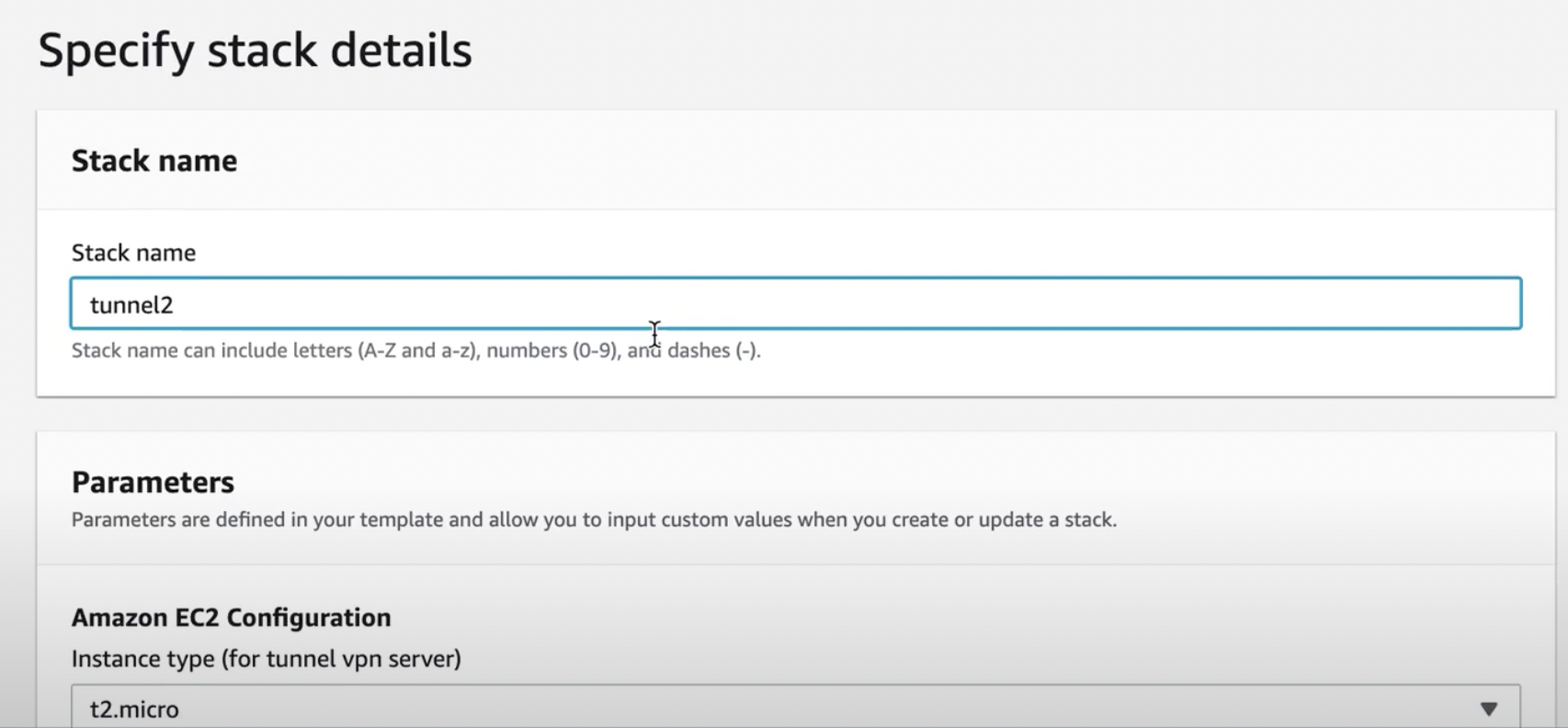
4. Specify stack details
Stack name, Instance type, SSH Key Name (SSH key access to the instance), VPC (must be the same as your source/destination) and Public Subnet (should belong to the same VPC)

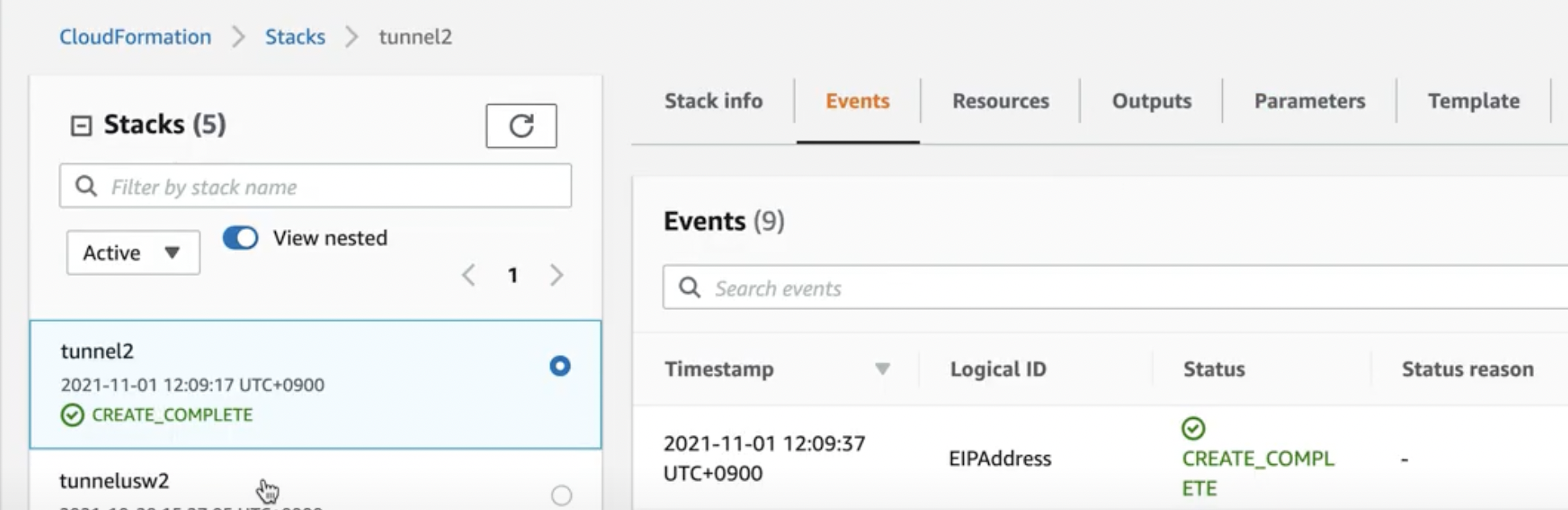
4. Wait for CloudFormation to build the infrastructure.
- An EC2 instance will be created on the specified VPC and Public Subnet to run the Secure Tunnel. We will attach a new Elastic IP and a new security group to allow ingress to ports 51820 (Secure tunnel listener port) and port 22 (SSH).
- Wireguard will be installed on the instance to set up our Secure Tunnel. Also, a cron job will be created to keep the tunnel connection open.
- When the setup of the instance is completed, it will automatically send the public IP address of the instance to Integrate.io to complete initial setup.
5. Once CloudFormation has completed, ensure the Integrate.io ELT & CDC dashboard shows the tunnel as Setup Complete and Active.
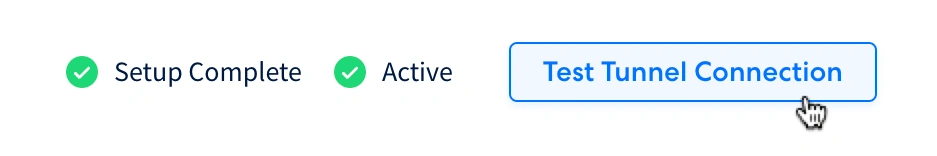
6. Test the tunnel connection to see if we can establish a connection with the tunnel.
Note: This test would only test the connection to the tunnel, not to the source/destination itself.
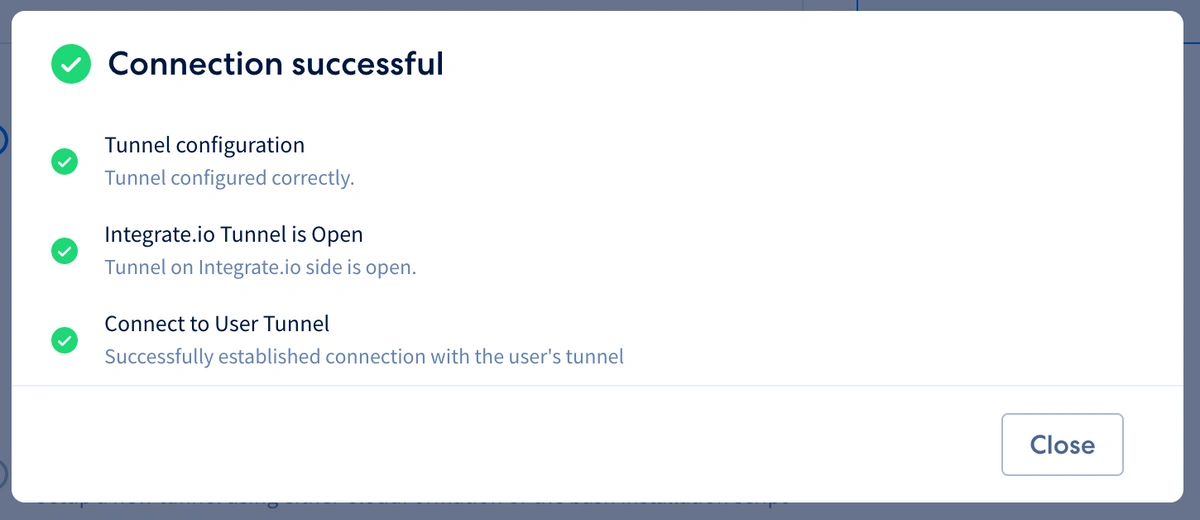
8. If the test is successful, continue with the source/destination setup.